Kiwa works together with Intigriti by leveraging their extensive platform of over 40 thousand independent security researchers and ethical hackers. Enable yourself to benefit of the skills, talent, time and creativity of a large and very experienced security audience. Based on your predefined scope these security researchers and ethical hackers will search for vulnerabilities. By leveraging the minds of the many and matching the most skilled and trusted researchers, companies will benefit of high quality vulnerability submissions.
Full control
Kiwa’s service allows you to have your assets tested in your own private bug bounty program on Intigriti’s platform. We deliver valuable security vulnerability reports which could in turn be beneficial for mending and (re)shaping the cybersecurity of your business or organisation. You as a customer are in full control and will be assisted by Kiwa in every step of the process to successfully complete the program.
Get valuable insights
The basis for the bug bounty program is straightforward: A crowd of ethical hackers and security testers will test your web and mobile applications or other internet connected assets with the intention to find security flaws. The ethical hackers and security researchers are incentivised to perform the tests in the following manner: for every valid vulnerability found they get a reward, also called a bounty. The more severe a found vulnerability, the higher the reward or bounty. This allows for hackers to make full use of their creativeness in order to earn good rewards. If they find a vulnerability they get rewarded whereas your business or organisation gets hold of critical information on a potentially harmful cyber risk. A win-win situation.
Kiwa guides you through every step
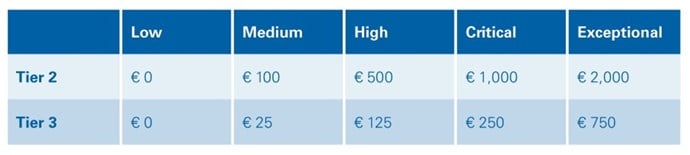
Kiwa guides you through every step of setting up and launching a successful bug bounty program on Intigriti’s platform. The bug bounty program has a testing period of four to six weeks in which your assets will be security tested according to your preferences and particular requirements. You are in total control of the total amount of available bounty, the bounty table (which contains the different amounts of bounties), the type of researchers and ethical hackers making up the pool of testers etc. The test results and outcomes are also followed up by Kiwa in a report and a debriefing meeting. In the end you will have enough information at hand to improve the security of your asset.
What does a Bug Bounty Security Testing program look like?
Kiwa and Intigriti’s program has six important milestones through which we guide and assist you. These milestones are:
What types of assets can be considered?
First and foremost the assets should be available through the internet. The ethical hackers and researchers use the internet to get access to the assets to further test and look for vulnerabilities. Besides this there are a few more topics we consider to select your assets for a bug and bounty program. Some examples are:
- The asset is in ownership by you but could be managed by a third party.
- When the asset is compromised the consequences could be impactful.
- Test environments and acceptance environments.
- Discovering vulnerabilities for the asset brings value regardless of the impact of the consequences.
- Testing credentials, etc.
Included in this program are:
- One program (test period = 4-6 weeks);
- Approximately 25 reports;
- Kiwa test summary report (after test period);
- 40 handpicked security researchers (ID checked).
Why Kiwa?
Kiwa is a trusted and independent third party that performs tests to provide the basis for guaranteed quality. Together with Intigriti we offer you a bug bounty service which allows for a thorough check-up of the web and cybersecurity of your assets. As systems and organisations are digitalising so do our means of testing and inspecting. As cybersecurity is an important cornerstone of our digital age, Kiwa is heavily involved in providing high quality, useful penetration tests and services. We are your partners for progress!